Run agents in production. Not in fear.
Before your agent touches money, data or production, one in-process Kernel decides what runs, verifies the intent behind it, and encrypts the data the agent shouldn't see.
Decisions enforced. Intent anchored. Data sealed.
A single SDK call around any consequential agent action. Behind it, three checks run before execution. Identical on every Kernel install, signed for every audit.
Immutable. Always runs first.
Cannot be configured off. Kernel covers the full OWASP Agentic Top 10 by default, runs before any policy check, cannot be configured away, and anchors agent intent at creation so mid-session manipulation is caught before execution.
Hidden instructions in input data redirect agent actions.
Agent invokes a tool in a way it wasn't authorized for.
Agent extracts sensitive data and routes to unauthorized destination.
Attacker contaminates agent memory to influence future decisions.
Mid-session manipulation that shifts the agent's objective.
Runaway loops or attacker-induced calls drain API budgets.
Agent's system prompt exfiltrated through crafted inputs.
Compromised dependency injects malicious behavior.
Attacker spoofs an agent's identity to act on behalf of trusted agents.
One bad agent decision propagates through dependent agents downstream.
 Why open-source guardrails alone aren't enough for regulated production.
Why open-source guardrails alone aren't enough for regulated production.
Microsoft published the Agent Governance Toolkit under the MIT License in April 2026. Here's what it covers, and the five gaps regulated fintechs hit in production.
Read the postEvery action checked against declared intent.
The most sophisticated attacks are agents manipulated mid-session. Kernel anchors agent intent at creation. Mismatch is caught before execution.
When the agent is created, it declares its purpose and the actions allowed within that purpose. Kernel stores this intent immutably for the agent's lifetime.
Before every action, Kernel checks the action against the agent's declared intent. Matches proceed. Mismatches are stopped at the intent layer, regardless of what the agent thinks it should do.
Every intent mismatch is logged with the action attempted, the declared intent, and a possible-compromise flag. This is your earliest signal that an agent is being manipulated.
Your agent cannot leak what it never saw.
Kernel sits between your data and the agent's context. Each sensitive field is protected at the level you choose:
- readable plaintext where the agent needs to reason.
- an opaque token where it only needs to reference.
- or sealed ciphertext where the agent is a courier and nothing more.
The agent still does the job. The data stays under cryptographic control end-to-end.
Credentials never leave your infrastructure. Data never leaves your process. Private keys never leave your KMS.
Limits you set. Policies you shape.
Two layers shaped by you. Enforced by Kernel. Signed in the same audit trail.
Per-agent class. Configurable thresholds.
Agents don't take breaks. A runaway loop, an unexpected input, or a mid-session compromise can burn through your API budget, process unauthorized transactions, or generate cascading errors, all while you're asleep.
Group your ephemeral agents under a control group policy. Configure quotas, budgets, and circuit breakers per group, not per agent.
Your business logic, declared.
Describe your agent in plain English. Kernel generates a YAML/Rego policy.
Kernel ships with pre-built policy templates for the most common regulated agent types. For everything else, describe what your agent does in plain English. Kernel's Policy Agent turns it into a validated, production-ready policy. A human reviews before anything goes live.
When any limit is hit, the agent doesn't slow down. It stops.
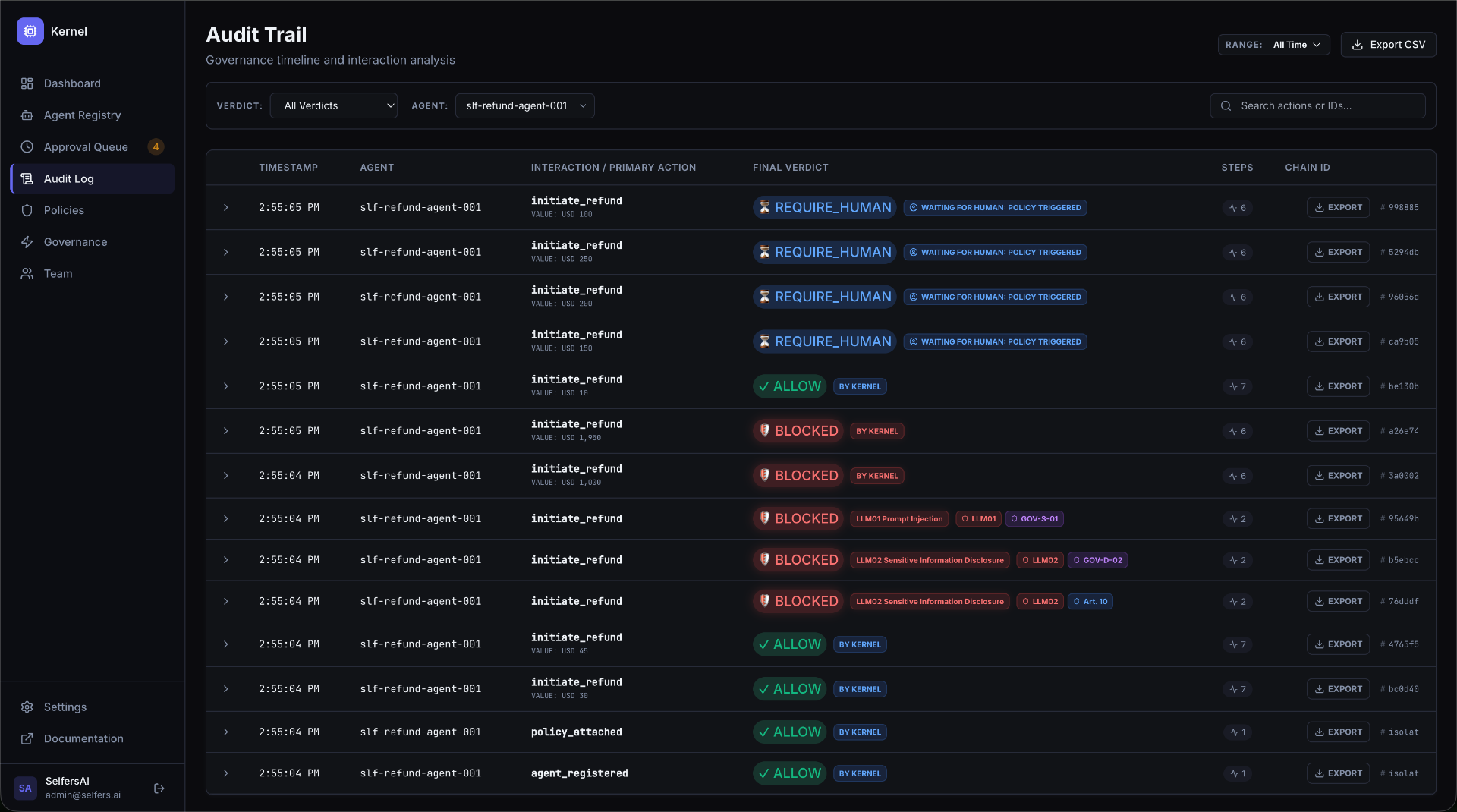
Audit & Reporting
Every Kernel decision is logged immutably in under a millisecond. Not just the verdict, which governance layer triggered, what the agent declared, which OWASP risk applies, who approved it, the full execution chain.